Cellular V2X Communication Overview
4G/LTE based communications
DSRC is a major technology to enable the mass deployment of V2X communications. However, the DSRC technology has some major drawbacks, such as important transmission latency, low scalability and short coverage range, in the order of the kilometer. However, using 4G/TLE based technology can have massive advantages. In fact, the technology used for vehicle communications will be the same as the one used for cellular communications, meaning that the same equipment and most of the protocols can be used. This situation is a significant benefit, especially considering that: i) more and more vehicles are coming with built-in cellular technology, ii) the technical details (specifications) are constantly being updated and improved, and iii) there’s already a large network of cell phone towers (base stations) in place.
Based on that, Cellular based V2X communication can be a much better alternative, giving that it has a larger coverage and higher transmission capabilities. The general security architecture can be seen below [1]. Security Architecture for V2X communication based on LTE :
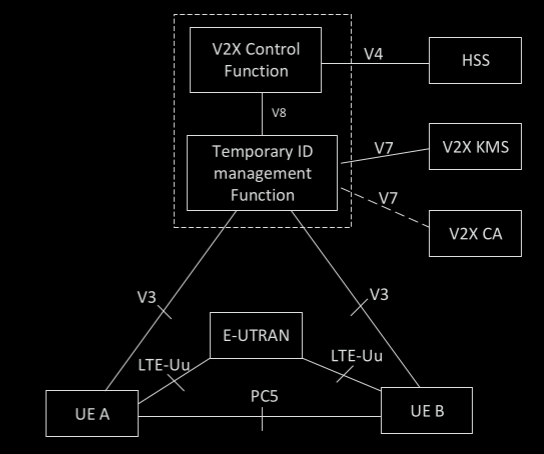
Here are explained all the building blocks presented in the architecture [1] :
- V2X Control Function (VCF): The V2X Control Function serves as the principal management component for V2X-related services within a network. Its role includes facilitating network-related activities, such as supplying the User Equipment (UE) with the essential parameters for utilizing V2X communications.
- Home Subscriber Server (HSS): It is a crucial component within the core networks of LTE, functioning as a central user database consolidated within a singular node.
- Temporary ID Management Function (TIMF): This entity is responsible for providing temporary IDs to UEs or vehicles. The use of temporary IDs is crucial in V2X communications to ensure privacy and security.
- V2X Key Management Server (V2X KMS): This server manages the cryptographic keys used in the V2X communication system. V2X Certificate Authority (V2X CA): Similar to CAs in traditional IT systems, the V2X CA is responsible for issuing digital certificates to entities within the V2X network.
- E-UTRAN (Evolved Universal Terrestrial Radio Access Network): This is part of the LTE (Long Term Evolution) network architecture. It’s the air interface of 3GPP’s LTE and provides high-speed data and voice communications.
- LTE-Uu: Interface between mobile devices and the LTE network for traditional cellular communications
- PC5: Direct communication interface between devices, primarily used for low-latency applications.
V2I communications uses LTE-Uu whereas V2V and V2P communications uses PC5. 3GPP (3rd generation partnership project) introduced ProSe (Proximity Services) in release 12 to enable communication over short distances using a sidelink, which is a direct communication link, based on PC5. In release 14, 3GPP extended the functionality of ProSe by utilizing the LTE-Uu interface - which uses uplink/downlink, as opposed to PC5 who uses sidelink - and the updated PC5 interfaces. The updated PC5 interfaces works in two different modes which are mode 3, scheduled resource allocation mode, and mode 4, autonomous resource selection mode.
- Mode 3: V2X communication uses sidelinks with the help of base stations that does the scheduling (i.e. controlled by the network).
- Mode 4 : V2X communication uses sidelinks with sidelink resources selection automatically done by the vehicles. Therefore, mode 4 is capable of functioning independently of cellular coverage, making it the fundamental mode for Vehicle-to-Vehicle (V2V) communication. This is because safety applications must not rely on the presence of cellular network availability.
UE authentication is controlled by the VCF and the HSS. Lastly, the distribution of temporary credentials and IDs are done through the TIMF.
It is important to note that the UE have to be authenticated to the LTE server before starting any V2X activity. If the UE is not authenticated, radio resources may be allocated to malicious UEs, which can reduce the availability for legitimate UEs. This reduction in availability can even lead to a DoS attack. In addition, the user needs to authenticate the server to prevent the possibility that an attacker may act as a fake server.
Physical Details
LTE-V uses SCFDMA (single-carrier frequency-division multiple access) and can support 10 and 20 MHz channels. Channels are divided into three main components : subframes (which are 1 ms long, as the transmission time interval), resource blocks (RBs), and subchannels. The smallest unit of frequency that can be given to a single user are resource block (RB). The width of this unit is 180 MHz in frequency. A combined group of RBs (which can vary) in the same subframe are called a subchannel, per the LTE-V definition, and are used as a transmission channel for data and control information. The actual exchanged data are encapsulated in transport blocks (TB), and are transmitted over PSSCH, or physical sidelink shared channels. Regarding the sidelink control information (SCI), which encapsulate the control data, they are transmitted over PSCCH, or physical sidelink control channels. Every node that wants to transmit a TB has to transmit a SCI alongside. The SCI contains important information that every nodes has to get in order to receive and decode the TB. It mainly consists of modulation and coding scheme (MCS) and the different RBs used, among others. A TB and its SCI have to be transmitted in the same subframe.
The term SCI + TB is used to describe the scenario where an SCI and the TB it is associated with are transmitted within the same subframe, scenario that LTE-V defines in two different schemes as seen in the figure below [2]:
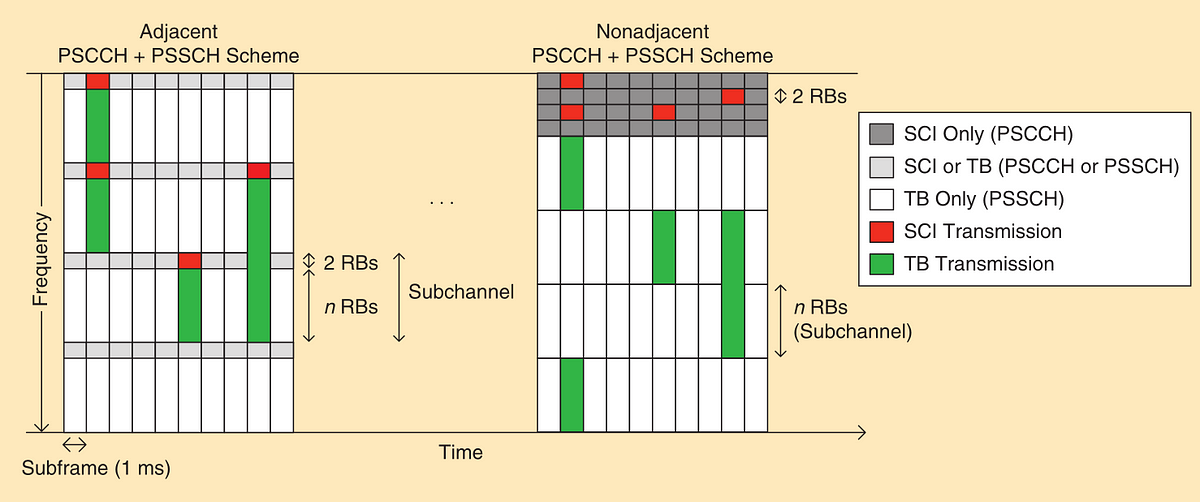
- Adjacent PSCCH + PSSCH: The SCI and TB are sent using RBs right next to each other. In every SCI + TB transmission, the SCI takes up the first two RBs in the initial subchannel used for sending. The TB is sent right after the SCI in the subsequent RBs and might use multiple subchannels based on how large it is. If it spreads over multiple subchannels, it will also use the first two RBs of those additional subchannels.
- Nonadjacent PSCCH + PSSCH: The RBs are split into groups called pools. There’s a specific pool set aside exclusively for sending SCIs, which take up two RBs. Another separate pool is used solely for transmitting TBs, and this pool is further organized into smaller segments known as subchannels.
5G based communications
The 3GPP has initiated the development of advanced 5G V2X features as part of Release 15, finalizing the study of new use cases and the corresponding requirements to be supported. Release 15 shifts the focus towards autonomous driving functionalities, such as vehicle platooning, exchanging sensor and map data, sharing information pertinent to partially/conditionally and highly/fully automated driving, as well as remote driving, among others.
A conceptualized architecture is proposed in [3], constructed on top of 3GPP architecture. It mainly introduces the “Security Reflex Function (SRF)” to strengthen 5G-V2X networks by enabling dynamic security and efficient mobility management for the expected communication of cellular-supported vehicles requiring constant connectivity. SRF offers network adaptability and access management by enabling edge-based authentication, therefore offloading core network tasks and enhancing response times. It employs partial-key allocations for individualized device security and supports on-demand gNB, converting stationary vehicles into network nodes to facilitate versatile and emergency networks. Additionally, SRF manages network slicing and anonymity by generating short-term, mode-specific keys, and provides user-side secondary authentication for vehicles used as access points, optimizing routing while maintaining end-to-end security. Its multi-radio support centralizes communication across various radio interfaces, ensuring secure, cost-effective connectivity. As a multi-functional, agile component of the 5G-V2X architecture, SRF is essential in maintaining secure and continuous connectivity.
5G-V2X technology, representing the cutting-edge of vehicle-to-everything communication, remains an important and recent area of research in the scientific community. Despite significant advancements, researchers continue to explore the potential it holds, focusing on enhancing connectivity, security, and efficiency.
References [1] : Shanzhi Chen et al. “Vehicle-to-Everything (V2x) Services Supported by LTE-Based Systems and 5G”. In: IEEE Communications Standards Magazine 1.2 (2017), pp. 70–76. issn: 2471–2825, 2471–2833. doi: 10.1109/MCOMSTD.2017.1700015. [2] : Rafael Molina-Masegosa and Javier Gozalvez. “LTE-V for Sidelink 5G V2X Vehicular Communications: A New 5G Technology for Short-Range Vehicle-to-Everything Communications”. In: IEEE Vehicular Technology Magazine 12.4 (Dec. 2017), pp. 30–39. issn: 1556–6072. doi: 10.1109/MVT.2017.2752798. [3] : Vishal Sharma, Ilsun You, and Nadra Guizani. “Security of 5G-V2X: Technologies, Standardization, and Research Directions”. In: IEEE Network 34.5 (2020), pp. 306–314. doi: 10.1109/MNET.001.1900662.
Author : Said Eddak
